Somali.A
Summary
Somali.A is a mass-mailing worm that terminates security-related processes and blocks antivirus-related software updates. This malware will only run on Windows platforms that have .NET framework installed.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Upon execution, Somali.A creates the following auto-run registry key so that every time the user logs on, Somali.A will be executed:
- [HKCU\Software\Microsoft\Windows\Currentversion\Run] Services32.bak = %windi%\system32\ctfmon32.exe
It then drops several copies of itself:
- %windir%\system32\ctfmon32.exe
- %rootdir%\project.pif
- %currentdir%\Project-setup.exe
For its signature, it creates the following registry key:
- [HKCU\MadSoli] MadSoli = "System"
It creates a Mutex named MadSoli so that there will be only one instance of itself in the memory.
It displays the following fake error messages:
Note: This message will appear on the first run on a clean machine.

Note: This message will appear if it has been run previously.
Somali.A checks the running processes and terminates processes with the following strings:
- AVGSERV
- AVGSERV9
- Clshield
- DAP
- GhostTray
- mghtml
- NAVW32
- notepad
- NTPROTECTED
- regedit
- scan32
- SCAN95
- taskmgr
Somali.A can also propagate through network. It does this by creating the Shared folder:
- %rootdir%\System33
- and drops a copy of itself on the said shared folder as Sound.exe.
The said shared folder has a share name of MadSoli, please see the sample image below:
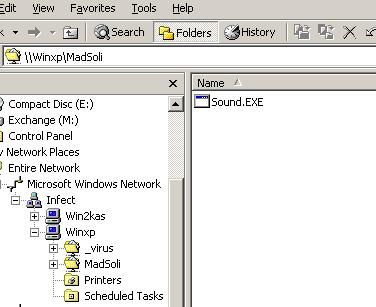
Subsequently, it will create the following registry key:
- [HKLM\System\CurrentControlSet\Services\lanmanserver\Shares] MadSoli = {Multi-String} - See Screenshot:
Somali.A creates a HOST file named HOST.file in the %windir%\system32\drivers\etc directory.
This HOST file will not allow accesses to the following sites:
- avg.com
- download.mcafee.com
- google.com
- google.com
- mcafee.com
- pandasoftware.com
- symantec.com
- trendmicro.com
- update.symantec.com
- www.24-7-transportation.com
- www.adhdtests.com
- www.aegee.org
- www.aimcenter.net
- www.alupass.lu
- www.amanit.ru
- www.AmirCivil.com
- www.andara.com
- www.angelartsanctuary.com
- www.anthonyflanagan.com
- www.approved1stmortgage.com
- www.argontech.net
- www.asianfestival.nl
- www.atlantisteste.hpg.com.br
- www.avg.com
- www.avg.com
- www.aviation-center.de
- www.bbc.com
- www.bbsh.org
- www.bga-gsm.ru
- www.boneheadmusic.com
- www.bottombouncer.com
- www.bradster.com
- www.buddyboymusic.com
- www.bueroservice-it.de
- www.calderwoodinn.com
- www.capri-frames.de
- www.celula.com.mx
- www.ceskyhosting.cz
- www.chinasenfa.com
- www.cntv.info
- www.compsolutionstore.com
- www.coolfreepages.com
- www.corpsite.com
- www.couponcapital.net
- www.cpc.adv.br
- www.crystalrose.ca
- www.cscliberec.cz
- www.curtmarsh.com
- www.customloyal.com
- www.DarrkSydebaby.com
- www.deadrobot.com
- www.dontbeaweekendparent.com
- www.download.mcafee.com
- www.dragcar.com
- www.ecofotos.com.br
- www.eurostavba.sk
- www.everett.wednet.edu
- www.fcpages.com
- www.featech.com
- www.FritoPie.NET
- www.google.com
- www.mcafee.com
- www.microsoft.com
- www.my-etrust.com
- www.pandasoftware.com
- www.symantec.com
- www.trendmicro.com
- www.update.symantec.com
- www.viruslist.com
- www.yahoo.com
- yahoo.com
Somali.A attempts to mass-mail itself using mx4.mail.yahoo.com as its SMTP server.
It searches for Yahoo! email addresses on Windows folder in the files with the following extension names:
- adb
- asp
- cfg
- cgi
- dbx
- eml
- html
- pl
- shtm
- txt
- wab
- xml
Possible Email address of the Sender:
- antiblaster@yahoo.com
- avg@yahoo.com
- bill@yahoo.com
- bob@yahoo.com
- ebook@yahoo.com
- info@yahoo.com
- iraq@yahoo.com
- LongShot@yahoo.com
- matt@yahoo.com
- mcafee@yahoo.com
- nod32@yahoo.com
- panda@yahoo.com
- smith@yahoo.com
- stan@yahoo.com
- steve@yahoo.com
- symantec@yahoo.com
- update@yahoo.com
- YourFriend@yahoo.com
- CC: software@yahoo.com
- BCC: crack@yahoo.com
Possible Subjects:
- Announcement
- ANTI VIRUS
- Attention
- email account disabling warning
- FBI
- IranSare2008
- mcafee
- NOD32
- password
- Read it immediately
- Soccer funs in public place
- symantec
- Text Message
- Text message
- Yahoo!
- Your IP was logged
Possible Message Body:
- Your email account was used to send a huge amount of unsolicited spam messages during the recent week. If you could please take 5-10 minutes out of your online experiences and confirm the attach document so you will not run into any future problems with the online service.
- It has come to our attention that your (File!) User Profile ( x )records are out of date. For further details see the attached document. Tank you for using !
- Thank you for using file
- +++ Attachment: No Virus (Clean)
- +++[mcafee] Antivirus - www.mcafee.com
- Deliver Error
- Message Error
- help attached
- such as yours
- illegal st. of you
- I have your password!
- classroom test of you?
- old photos about you?
Backdoor
Somali.A opens TCP port 8051. If a remote hacker connects to the said port and sends strings through this port, Somali.A will reply with the same string with all capital letters and adds exclamation mark at the end of the string.
Payloads
Somali.A creates the following user in the local User Group:
User name: NewAdmin Password: MadSoli Comment: Windows pc
Note: Run the following command from the CMD prompt to check for the said user: "net user NewAdmin".
It deletes all the subkeys on the following registry key:
- [HKCU\Printers]
- and displays the following Message Box every 19th of the month:
