Trojan-Downloader:W32/Small.DOG
Summary
This type of trojan secretly downloads malicious files from a remote server, then installs and executes the files.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Trojan-Downloader:W32/Small.DOG secretly downloads malware from a remote site to install and execute on the infected machine.
Distribution
Small.DOG may be delivered to the system in an infected file attachment accompanying German-language spam email messages, such as below:
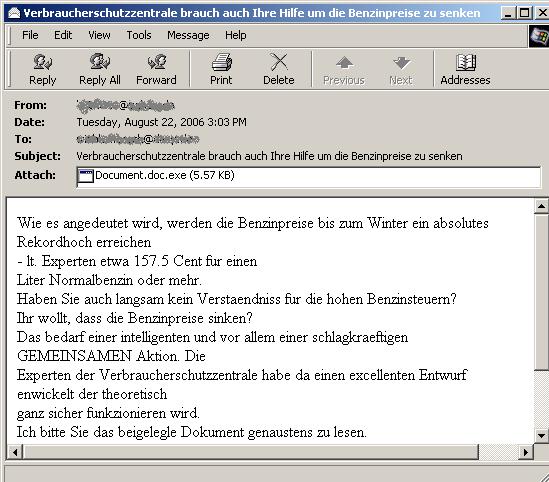
The attachment name used is Document.doc.exe. The attachment uses the Microsoft Word icon to disguise its executable nature and deceive the user into believing the attachment is a word document:

Execution
If the user executes the malware by clicking on the attachment, the Trojan creates a new instance of Svchost.exe using itself as the parameter.
It then drops the following file in the Windows System folder:
- {Copied filename of any file found on the Windows System directory}{Random character}.exe
Small.DOG attempts to connect to one of the following websites to download an encrypted text file:
- http://81.95.147.138/[...].txt
- http://docslv.com/gallery/bridge/[...].txt
- http://dreadwolf.net/[...].txt
- http://dynafilmes.com.br/imagens/3/[...].txt
- http://feldvossundpartner.de/images/[...].txt
- http://jobundfit.de/images/[...].txt
- http://leads4sales.co.uk/images/main/[...].txt
- http://mkpicture.de/images/[...].txt
- http://soloaguia.com/imagens/[...].txt
- http://spbfp.atlant.ru/sys/[...].txt
- http://spbfp.atlant.ru/sys/sys/[...].txt
- http://trendbusiness-at-home.de/images/[...].txt
It then decrypts the downloaded text file to reveal the following download path:
- apte-hamburg.de/Deutsch/Aktuell/{...}.exe
Small.DOG will then download and execute this file. The downloaded file is detected as Trojan-Spy:W32/BZub.BL
RegistryIt installs the following registry entries as its autostart technique:
- [HKEY_CURRENT_USER\SYSTEM\CurrentControlSet\Control\Lsa] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName%.exe"
- [HKEY_CURRENT_USER\Software\Microsoft\OLE] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName%.exe"
- [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName%.exe"
- [HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunServices] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName%.exe"
- [HKEY__MACHINE\SOFTWARE\Microsoft\Ole] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName%.exe"
- [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunServices] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName%.exe"
- [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName%.exe"
- [HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Lsa] {Special Character}:=7<${Special Character}#72'6S = "C:\%WinDirSys%\%FileName% .exe"
Note: %WinDirSys% is by default C:\Windows\System32 and %FileName% represents the Copied filename plus the Random character.