Rootkit:W32/ZAccess
Summary
Rootkit:W32/ZAccess constantly displays advertisements on the infected machine and may silently contact remote servers to retrieve additional advertising information.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
Manual action
Perform a full scan of the computer system with the F-Secure security program to find and disinfect the relevant files. Before scanning, enable the product to scan system files by following these steps:
- In the F-Secure product, go to "Settings"
- Go to "Manual scanning"
- Uncheck "Scan only known file types"
Then perform a full computer scan.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
Rootkit:W32/ZAccess is distributed in programs disguised as a cracked copies of legitimate commercial software (a distribution method more commonly seen with trojans). It may be distributed via pornography websites. It has also been reported as being distributed via compromised legitimate websites.
Once installed, ZAccess will display unsolicited advertisments on the machine and redirects the web browser to unsolicited advertisement websites. In order to do the latter, the malware may contact remote servers to retrieve additional advertising information; the specific URLs contacted are varied, but the top level domain is always .CN.
Installation
On installation, the malware will replace a system driver (in the location %WINDIR%\system32\drivers) with a copy of its rootkit driver. Selection of a system driver to replace is done using an internal algorithm. The rootkit will display the contents of the original system driver, presumably to camouflage its presence on the system.
The malware then creates a hidden, encrypted volume which is used to store the original system driver file that was replaced, as well as other component files used by the malware. The hidden volume has the following format:
- %WINDIR%\$NtUninstallKB{5_digits}$
It also creates a zero byte Alternate Data Stream file in %WINDIR%\{numbers_only_file} which will be silently executed and run in the background:
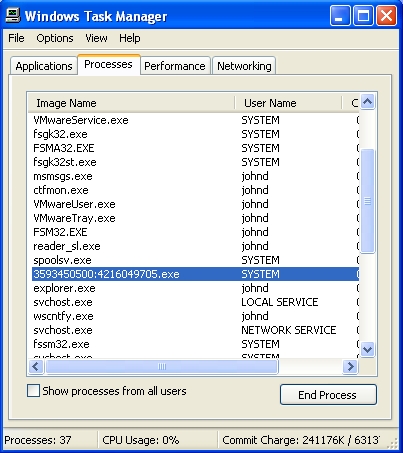
Some variants of this malware will drop other component files in the following location:
- %USERPROFILE%\Local Settings\Application Data\number_only_folder
)
Protect your devices from malware with F‑Secure Total
Protecting your devices from malicious software is essential for maintaining online security. F‑Secure Total makes this easy, helping you to secure your devices in a brilliantly simple way.
- Award-winning antivirus and malware protection
- Online browsing, banking, and shopping protection
- 24/7 online identity and data breach monitoring
- Unlimited VPN service to safeguard your privacy
- Password manager with private data protection
More Support
Community
Ask questions in our Community .
User Guides
Check the user guide for instructions.
Submit a Sample
Submit a file or URL for analysis.