Licat.C
Summary
Licat.C, a variant of Licat, is a Trojan. Licat.C can send instant messages or contact certain websites to inform malware authors about certain events and allows downloading files on the infected computer. Licat.C tries to connect to certain websites on Internet.
Removal
Based on the settings of your F-Secure security product, it will either move the file to the quarantine where it cannot spread or cause harm, or remove it.
A False Positive is when a file is incorrectly detected as harmful, usually because its code or behavior resembles known harmful programs. A False Positive will usually be fixed in a subsequent database update without any action needed on your part. If you wish, you may also:
-
Check for the latest database updates
First check if your F-Secure security program is using the latest updates, then try scanning the file again.
-
Submit a sample
After checking, if you still believe the file is incorrectly detected, you can submit a sample of it for re-analysis.
Note: If the file was moved to quarantine, you need to collect the file from quarantine before you can submit it.
-
Exclude a file from further scanning
If you are certain that the file is safe and want to continue using it, you can exclude it from further scanning by the F-Secure security product.
Note: You need administrative rights to change the settings.
Technical Details
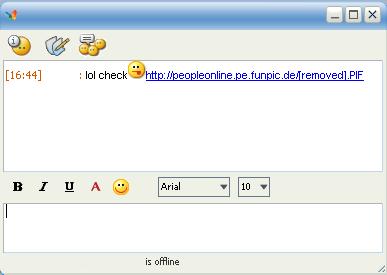
Licat.C arrives on the system as a downloaded file via a link that is spammed through MSN Messenger. Below is a sample message:
It searches for the location of MSN Messenger installed on the system through the following registry key:
- [HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\MSNMSGR.EXE\Path]
When found, it attempts to rename the original MSN Messenger application client to msgs.exe. It then copies itself to the folder using the filename msnmsgr.exe so that it will start each time that MSN Messenger is started by the user. The copy then launches the renamed Messenger file.
Licat.C's backdoor component (some instances are detected as Backdoor.Win32.MSNMaker.v) connects to the following website:
- https://go.cheap[REMOVED].info/
- http://go.links4[REMOVED].biz/
This websites contains links to the following malicious IP address:
- 69.64.38.140
It uses a vulnerability in the meta tag, which has a malicious IP address on its content. Vulnerable web browsers will automatically execute the file when this site is accessed.
When this IP address is accessed, it will again download from the following websites and execute other malware on the system using the following filenames:
- https://www.uglyphotos.net/[REMOVED] - alfa.exe
- https://www.uglyphotos.net/[REMOVED] - sprT.exe
- https://www.uglyphotos.net/[REMOVED] - Xinstall.exe
- lol check:P http://peopleonline.pe.funpic.de/[removed].PIF
When this URL link is clicked, a copy of Licat.C will be downloaded on the system.
The two other downloaded files are a trojan dropper (Xinstall.exe) and an adware application (alfa.exe) respectively. They are now detected asTrojan-Dropper.Win32.PurityScan.ag and not-a-virus:AdWare.Win32.Softomate.q.